
Aqua Nautilus researchers shed light on a Linux malware, dubbed perfctl malware, that over the past 3-4 years targeted misconfigured Linux servers.
The malicious code was used to drop cryptocurrency miners and proxyjacking software.
Perfctl is an elusive and persistent malware targeting Linux servers, it employs rootkits to conceal its presence and halts any “noisy” activities when a new user logs in, lying dormant until the server is idle again. For communication, it uses a Unix socket internally and TOR externally. Upon execution, perfctl deletes its binary and operates in the background as a service.
Despite the malware’s primary goal being to run cryptominers, experts warn that it also executes proxyjacking software. In one sandbox test, a threat actor accessed the malware’s backdoor for reconnaissance purposes. The attackers analyzed the server and deployed utilities to investigate its environment and better understand how their malware was being studied.
Once attackers exploited a vulnerability or misconfiguration, the perfctl malware downloads the main payload from an attacker-controlled HTTP server. The payload employs multiple layers to ensure persistence and evade detection. It moves itself to the /tmp directory, renames itself after the process that executed it (e.g., sh), and deletes the original binary to cover its tracks. The malware acts as both a dropper and a local command-and-control (C2) process, attempting to exploit the Polkit vulnerability CVE-2021-4043 (aka PwnKit) for root access.
The malicious code copies itself to various disk locations using deceptive names, establishes a backdoor on the server for TOR communications.
The malware drops a rootkit alongside modified Linux utilities (e.g., ldd, lsof) that function as user-land rootkits.
The Linux malware is packed and encrypted to evade detection. It uses advanced evasion techniques like halting activity when detecting new users, the malicious code could also terminate the competing malware to maintain exclusive access to the infected system.
“As part of its command-and-control operation, the malware opens a Unix socket, creates two directories under the /tmp directory, and stores data there that influences its operation. This data includes host events, locations of the copies of itself, process names, communication logs, tokens, and additional log information. Additionally, the malware uses environment variables to store data that further affects its execution and behavior.” . “All the binaries are packed, stripped, and encrypted, indicating significant efforts to bypass defense mechanisms and hinder reverse engineering attempts. The malware also uses advanced evasion techniques, such as suspending its activity when it detects a new user in the btmp or utmp files and terminating any competing malware to maintain control over the infected system.”
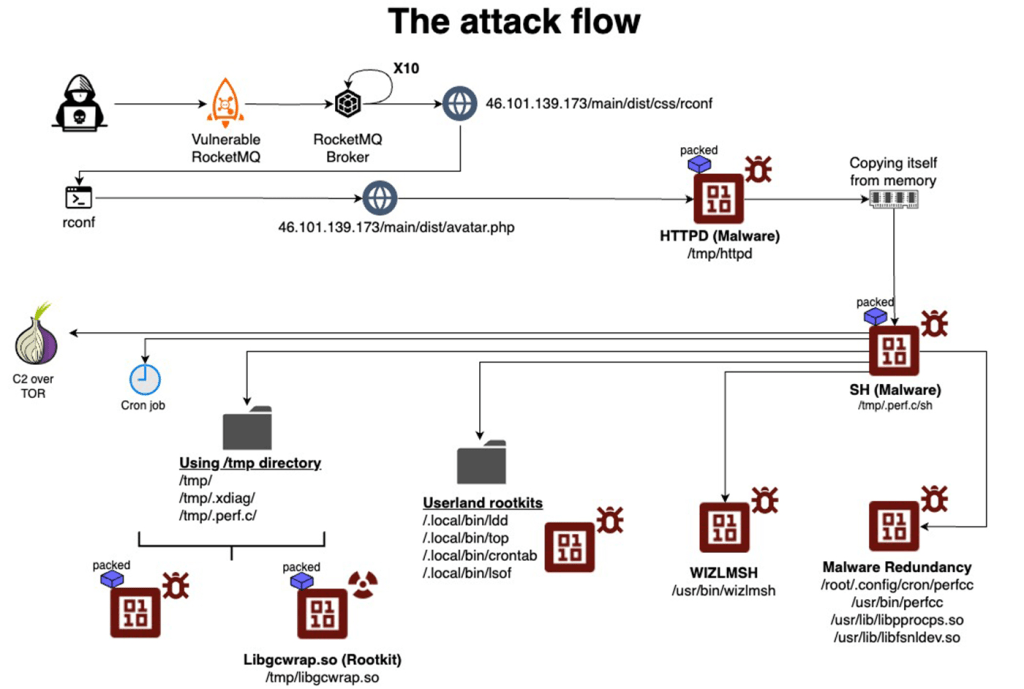
To maintain persistence, the attacker modifies the ~/.profile script to execute malware upon user login, checking if /root/.config/cron/perfcc is executable. If so, the malware runs before the legitimate server workload. It also executes the ~/.bashrc file in Bash environments to maintain normal server operations while the malware work in the background. The script suppresses errors to avoid warnings.
A small binary called wizlmsh (12kb) is dropped into /usr/bin, running in the background to ensure the persistence of the perfctl malware, verifying the execution of the main payload (httpd).
“The main impact of the attack is resource hijacking. In all cases we observed a monero cryptominer (XMRIG) executed and exhausting the server’s CPU resources. The cryptominer is also packed and encrypted. Once unpacked and decrypted it communicates with cryptomining pools.” concludes the report. “To detect perfctl malware, you look for unusual spikes in CPU usage, or system slowdown if the rootkit has been deployed on your server,” the researchers said. “These may indicate crypto mining activities, especially during idle times.”
Follow me on Twitter: and and Mastodon
(SecurityAffairs – hacking, Linux)