
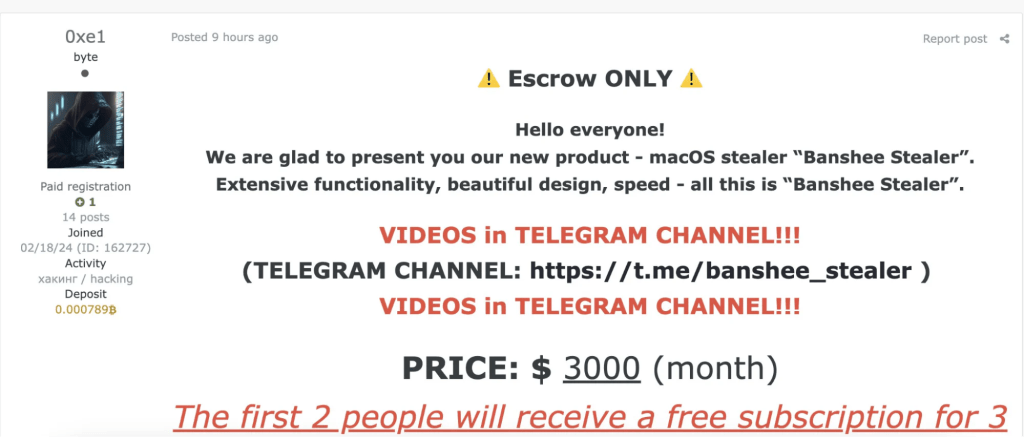
In August 2024, Russian crooks advertised a macOS malware called BANSHEE Stealer that can target both x86_64 and ARM64 architectures. The malware authors claim it can steal a broad range of data from compromised systems, including browser data, cryptocurrency wallets, and around 100 browser extensions.
BANSHEE Stealer employs basic evasion techniques, it relies on the sysctl API to detect debugging and checks for virtualization by running a command to see if “Virtual” appears in the hardware model identifier. Additionally, the malware avoids targeting systems where Russian is the primary language by it checking the user’s preferred language through the CFLocaleCopyPreferredLanguages API. However, these methods are simple and can be bypassed by advanced sandboxes and malware analysts.
The discovery of the malware highlights the growing focus on macOS-specific malware as the platform becomes a more frequent target for cybercriminals.
Researchers at Elastic Security Labs analyzed the malware and confirmed it can steal keychain passwords and data from multiple browsers.
Banshee Stealer can target data from nine different browsers, Chrome, Firefox, Brave, Edge, Vivaldi, Yandex, Opera, OperaGX, and Safari. The malware can collect cookies, logins and browsing history, but from Safari only cookies can be collected. Elastic researchers noticed that regarding Safari, only the cookies are collected by the AppleScript script for the current version.
“Additionally, data from approximately 100 browser plugins are collected from the machine. A list of these extension IDs is provided at the end of the blog post.” reads the report published by Elastic Security Labs. “The collected files are saved under <temporary_path>/Browsers.”
Banshee Stealer can also steal cryptocurrency from different wallets, including Exodus, Electrum, Coinomi, Guarda, Wasabi Wallet, Atomic and Ledger.
After collecting data, the malware compresses the temporary folder containing them into a ZIP file using the ditto command. The ZIP file is then XOR encrypted, base64 encoded, and sent via a POST request to a specified URL using the built-in cURL command.
“BANSHEE Stealer is macOS-based malware that can collect extensive data from the system, browsers, cryptocurrency wallets, and numerous browser extensions.” concludes the report. “Despite its potentially dangerous capabilities, the malware’s lack of sophisticated obfuscation and the presence of debug information make it easier for analysts to dissect and understand. While BANSHEE Stealer is not overly complex in its design, its focus on macOS systems and the breadth of data it collects make it a significant threat that demands attention from the cybersecurity community.”
Follow me on Twitter: and and Mastodon
(SecurityAffairs – hacking, malware)