
Yesterday, a joint law enforcement action, code-named Operation Cronos, conducted by law enforcement agencies from 11 countries disrupted the LockBit ransomware operation.
Below is the image of the Tor leak site of the Lockbit ransomware gang that was seized by the UK National Crime Agency (NCA).
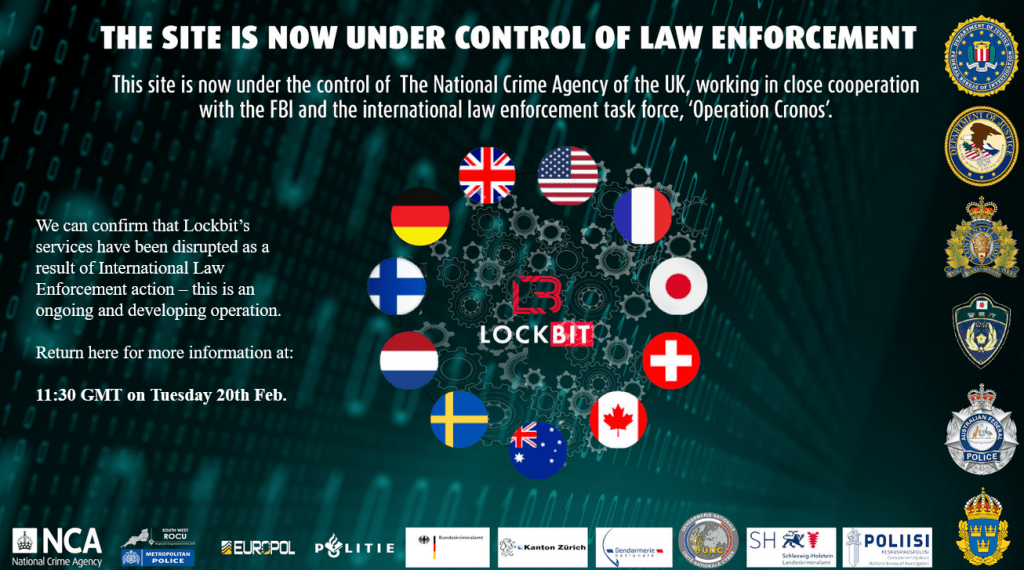
“The site is now under the control of law enforcement. This site is now under the control of The National Crime Agency of the UK, working in close cooperation with the FBI and the international law enforcement task force, ‘Operation Cronos’,” reads the banner.
“We can confirm that Lockbit’s services have been disrupted as a result of International Law Enforcement action – this is an ongoing and developing operation. Return here for more information at: 11:30 GMT on Tuesday 20th Feb”
The Operation Cronos operation is still ongoing and NCA announced that more information have yet to be shared.
“The site is now under the control of law enforcement. This site is now under the control of The National Crime Agency of the UK, Working in close cooperation with the FBI and the international law enforcement task force, Operation Cronos,” the banner reads.
“We can confirm that Lockbit’s services have been disrupted as a result of International Law Enforcement action – this is an ongoing and developing operation.”
vx-underground researchers contacted the administrators of the gang who confirmed that their infrastructure was seized by the FBI.
The operation led to the arrest of two members of the ransomware gang in Poland and Ukraine and the seizure of hundreds of crypto wallets used by the group.
The British NCA took control of LockBit’s central administration environment used by the RaaS affiliates to carry out the cyberattacks. The authorities also seized the dark web Tor leak site used by the group.
The Tor leak site was seized by the NCA and is now used to publish updates on the law enforcement operation and provide support to the victims of the gang.
The NCA also obtained the source code of the LockBit platform and a huge trove of information on the group’s operation, including information on affiliates and supporters.
Law enforcement also had access to data stolen from the victims of the ransomware operation, a circumstance that highlights the fact that even when a ransom is paid, the ransomware gang often fails to delete the stolen information.
“LockBit had a bespoke data exfiltration tool, known as Stealbit, which was used by affiliates to steal victim data. Over the last 12 hours this infrastructure, based in three countries, has been seized by members of the Op Cronos taskforce, and 28 servers belonging to LockBit affiliates have also been taken down.” reads the NCA’s announcement. “The technical infiltration and disruption is only the beginning of a series of actions against LockBit and their affiliates. In wider action coordinated by Europol, two LockBit actors have been arrested this morning in Poland and Ukraine, over 200 cryptocurrency accounts linked to the group have been frozen.”
The US Department of Justice for orchestrating ransomware attacks using the LockBit ransomware, they are currently in custody and will undergo trial in the US.
“The Justice Department also unsealed an indictment obtained in the District of New Jersey charging Russian nationals Artur Sungatov and Ivan Kondratyev, also known as Bassterlord, with deploying LockBit against numerous victims throughout the United States, including businesses nationwide in the manufacturing and other industries, as well as victims around the world in the semiconductor and other industries. Today, additional criminal charges against Kondratyev were unsealed in the Northern District of California related to his deployment in 2020 of ransomware against a victim located in California.” reads the published by DoJ.
“Finally, the Department also unsealed two search warrants issued in the District of New Jersey that authorized the FBI to disrupt multiple U.S.-based servers used by LockBit members in connection with the LockBit disruption.”
Additionally, the US authorities has unveiled indictments against two Russian nationals, accusing them of conspiring to carry out LockBit attacks.
The NCA and its global partners have secured over 1,000 decryption keys that will allow victims of the gang to recover their files for free. The NCA will reach out to victims based in the UK in the coming days and weeks, providing support to help them recover encrypted data.
“This NCA-led investigation is a ground-breaking disruption of the world’s most harmful cyber crime group. It shows that no criminal operation, wherever they are, and no matter how advanced, is beyond the reach of the Agency and our partners.” said National Crime Agency Director General, Graeme Biggar.
“Through our close collaboration, we have hacked the hackers; taken control of their infrastructure, seized their source code, and obtained keys that will help victims decrypt their systems.”
“As of today, LockBit are locked out. We have damaged the capability and most notably, the credibility of a group that depended on secrecy and anonymity.
“Our work does not stop here. LockBit may seek to rebuild their criminal enterprise. However, we know who they are, and how they operate. We are tenacious and we will not stop in our efforts to target this group and anyone associated with them.”
The free decryptor for the Lockbit ransomware can be downloaded from the website of the initiative. It’s unclear which version of the ransomware is targeted by the decryptor.
LockBit is a prominent ransomware operation . In 2022, LockBit was one of the most active ransomware groups, and its prevalence continued into 2023. Since January 2020, affiliates utilizing LockBit have targeted organizations of diverse sizes spanning critical infrastructure sectors such as financial services, food and agriculture, education, energy, government and emergency services, healthcare, manufacturing, and transportation. The LockBit ransomware operation operated under a Ransomware-as-a-Service (RaaS) model, recruiting affiliates to carry out ransomware attacks through the utilization of LockBit ransomware tools and infrastructure.
According to a joint report published by US authorities and international peers, the total of U.S. ransoms paid to LockBit is approximately $91M since LockBit activity was first observed in the U.S. on January 5, 2020.
Follow me on Twitter: and
(SecurityAffairs – hacking, ransomware)