
Cloudflare researchers discovered phishing campaign conducted by a Russia-linked threat actor FlyingYeti (aka UAC-0149) targeting Ukraine. The experts published a report to describe real-time effort to disrupt and delay this threat activity.
At the beginning of Russia’s invasion of Ukraine on February 24, 2022, Ukraine implemented a moratorium on evictions and termination of utility services for unpaid debt. The moratorium ended in January 2024, leading to significant debt liability and increased financial stress for Ukrainian citizens. The FlyingYeti campaign exploited this anxiety by using debt-themed lures to trick targets into opening malicious links embedded in the messages. Upon opening the files, the PowerShell malware COOKBOX infects the target system, allowing the attackers to deploy additional payloads and gain control over the victim’s system.
The threat actors exploited the WinRAR vulnerability CVE-2023-38831 to infect targets with malware.
Cloudflare states that FlyingYeti’s tactics, techniques, and procedures (TTPs) are similar to the ones detailed by Ukraine CERT while analyzing UAC-0149 cluster.
UAC-0149 targeted Ukrainian defense entities with COOKBOX malware since at least the fall of 2023.
“The threat actor uses dynamic DNS () for their infrastructure and leverages cloud-based platforms for hosting malicious content and for malware command and control (C2).” reads the published by Cloudflare. “Our investigation of FlyingYeti TTPs suggests this is likely a Russia-aligned threat group. The actor appears to primarily focus on targeting Ukrainian military entities.”
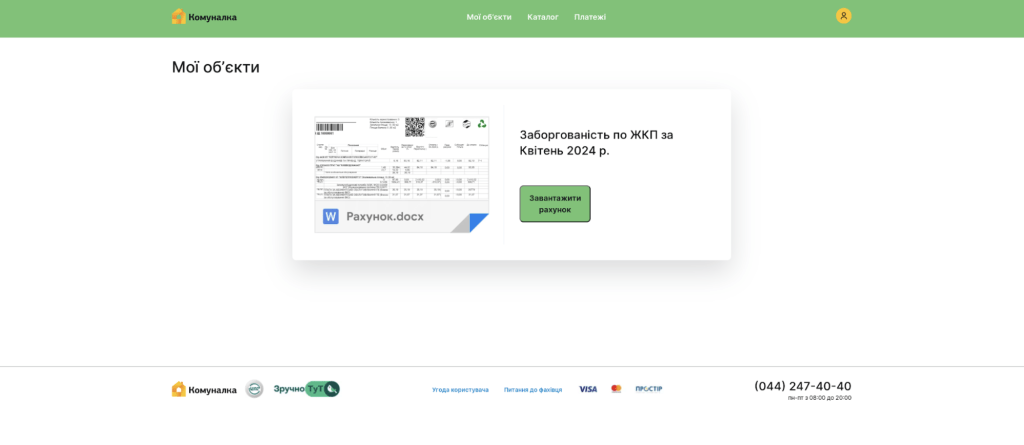
Threat actors targeted users with a spoofed version of the Kyiv Komunalka communal housing site (https://www.komunalka.ua), hosted on an actor-controlled GitHub page (hxxps[:]//komunalka[.]github[.]io). Komunalka is a payment processor for utilities and other services in the Kyiv region.
FlyingYeti likely directed targets to this page via phishing emails or encrypted Signal messages. On the spoofed site, a large green button prompted users to download a document named “Рахунок.docx” (“Invoice.docx”), which instead downloaded a malicious archive titled “Заборгованість по ЖКП.rar” (“Debt for housing and utility services.rar”).
Once the RAR file is opened, the CVE-2023-38831 exploit triggers the execution of the COOKBOX malware.
The RAR archive contains multiple files, including one with the Unicode character “U+201F,” which appears as whitespace on Windows systems. This character can hide file extensions by adding excessive whitespace, making a malicious CMD file (“Рахунок на оплату.pdf[unicode character U+201F].cmd”) look like a PDF document. The archive also includes a benign PDF with the same name minus the Unicode character. Upon opening the archive, the directory name also matches the benign PDF name. This naming overlap exploits the WinRAR vulnerability CVE-2023-38831, causing the malicious CMD to execute when the target attempts to open the benign PDF.
“The CMD file contains the Flying Yeti PowerShell malware known as COOKBOX. The malware is designed to persist on a host, serving as a foothold in the infected device. Once installed, this variant of COOKBOX will make requests to the DDNS domain postdock[.]serveftp[.]com for C2, awaiting PowerShell that the malware will subsequently run.” continues the report. “Alongside COOKBOX, several decoy documents are opened, which contain hidden tracking links using the service.”
The report also provide recommendations and Indicators of Compromise (IoCs).
Follow me on Twitter: and and Mastodon
(SecurityAffairs – hacking, FlyingYeti)